This is part 4 of 4 of the Personal Information Security Redux.
As you might imagine there is so much to the topic of personal information security. This series of articles has merely scratched the surface. Hopefully it will help you become less likely to become a victim of Malware, Viruses, Phishing or other mishaps. While working on the content it was obvious that there were lots of tools and concepts that deserve your consideration. Consider this the extra credit or perhaps icing on the cake if you’ve made it this far. Here are some other valuable tools, in no particular order:
- Ninite
- OpenDNS
- Spybot2
- Malware Bytes
- Foxit Reader
- Google Authenticator
- LastPass
- Eset Antivirus and Security Products
Ninite.com a hassle free place to install and update free software
When you first visit the Ninite website, it doesn’t look like much. Don’t let the no frills look fool you, Ninite is a must have in your personal information security portfolio for several reasons:
- You can install all the applications featured without user intervention.
- No “extras” are added on, just the software you request, no toolbars or extra goodies.
- You can run the installer later to update the applications.
Say you get a new computer and you want to add a few common applications. You go to ninite.com and check the boxes for those apps and it generates a single .exe file that can be used to install or update those apps. Its that simple.
Open DNS
A DNS server tells your computer the numerical address of a name. Open DNS uses this to provide an extra layer of protection to you by preventing you from accessing known Malware and phishing sites. It is very easy to take advantage of this service, you don’t even need an account (but having one gives you some cool advantages) you just have to use the OpenDNS servers. Go to their setup page for instructions on how to configure your device(s) to use OpenDNS.
Spybot 2 – Inoculate, Scan and Remove Malware and Viruses
Spybot2 is really handy in a few ways. One is the inoculation component, this protects your browser and system from some common Malware and Viruses. It also includes a scanner as well as a real time protection. It is most effective to use when you first get your windows computer or after a fresh installation/restoration of your operating system.
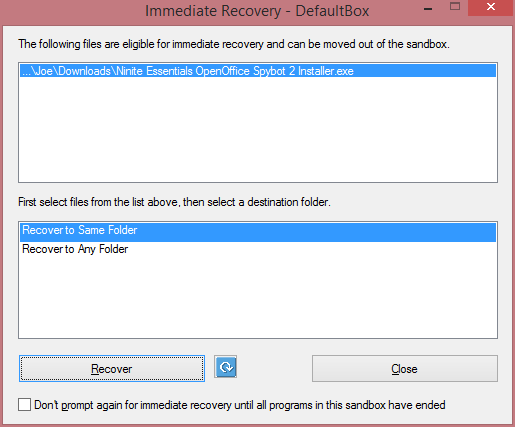
Advanced users: Ninite link to Spybot2 Installer.
Malware Bytes – Scan and Clean Malware and Viruses
Malwarebytes offers a real time scanner in their premium product, however it can be useful to just run a scan on your computer. Using different scanners (not real time protection!) combined can give you better peace of mind that your system is in good shape. Do not run multiple real-time protection products that do the same thing or it could bog down performance or worse.
Advanced users: Ninite link to MalwareBytes Installer.
Foxit Reader – Breaking the Chains from Adobe Acrobat Reader
Recently I wrote an article about my personal abandoning of Adobe Reader in favor of Foxit Reader. Adobe Reader is far too common of a target and frequently shows up on security notices. Unfortunately being the biggest player in a space also makes you the biggest target, and that certainly applies to Adobe Reader. You’re probably better off not taking the chance and having to worry about the constant updates and security patches necessary to secure Adobe Reader.
Advanced users: Ninite link to Foxit Reader Installer.
Google Authenticator
 Two Factor Authentication can help you in the event that somehow a password gets compromised. For example if you use LastPass and someone managed to get their hands on your master password, it would be useless to them if you use Two Factor Authentication with your LastPass account. The moment they tried to access the account they would receive a popup requesting the authenticator code. There is a good tutorial on setting this up over at How To Geek.
Two Factor Authentication can help you in the event that somehow a password gets compromised. For example if you use LastPass and someone managed to get their hands on your master password, it would be useless to them if you use Two Factor Authentication with your LastPass account. The moment they tried to access the account they would receive a popup requesting the authenticator code. There is a good tutorial on setting this up over at How To Geek.
LastPass “The Last Password You Have to Remember”
LastPass is a very useful application. Combined with Google Authenticator you can really improve your password quality. This will reduce the chance of having an account compromised through either a brute force (repetitive attempts to crack it) or dictionary (guesses based on common password combinations) attacks as each and every site you access has a unique and strong password. The “keys to the kingdom” is your master password, so take time to invest in making this both secure but also memorable.
Eset Antivirus and Security Products
Professionally I’ve been involved with Eset Products for quite some time. I always found them to be effective and not bad on system resources. I’ve written a lot about and mentioned Eset products in prior articles, here they are for added convenience:
A Closing Reminder
Remember that personal information security is about you. It’s about your web habits, what websites you use, how you setup your computer, and your commitment to understanding the threats that are out their. Don’t be lulled into a false sense of security by sales pitches for security products or by that free antivirus software your internet provider gave you. You are in control and you are responsible. Hopefully this series of articles has given you a boost in the right direction. Your comments and feedback are always welcome.